NETWORK SCANNING
Network Scanning:
Network scanning is the process of identifying and discovering open ports, services, operating systems, and other information on a target machine. This process helps in understanding the system's exposure and is often used by administrators for security assessments or by attackers for enumeration.TCP Communication Flags:
Synchronize (SYN):
The SYN flag is used to notify the transmission of a new sequence number. It initiates the connection process during a three-way handshake between two hosts.Acknowledgement (ACK):
The ACK flag confirms the receipt of data and identifies the next expected sequence number. When a packet is successfully received, the ACK flag is set to "1," indicating acknowledgment by the receiver.Push (PSH):
The PSH flag, set to "1," signals the sender to push data to the receiving application immediately. It is often raised at the start and end of data transfers to prevent buffer deadlocks.Urgent (URG):
The URG flag prioritizes urgent data processing. When set to "1," the system processes urgent data immediately, halting all other data processing.Finish (FIN):
The FIN flag indicates the termination of the connection. Setting it to "1" notifies the remote system that no more data transmissions will occur.Reset (RST):
The RST flag, set to "1," terminates a connection due to errors or unexpected issues. Attackers often use this flag during scans to identify open ports.SYN Scanning:
SYN scanning primarily uses the SYN, ACK, and RST flags to gather information from servers during enumeration. This technique is stealthy and effective for identifying live hosts and open ports.
NETWORK TOOLS SCANNING
Nmap (Network Mapper) is a versatile security scanner widely used for network exploration and penetration testing. It allows users to discover hosts, ports, services, and other network-related information. Nmap is beneficial for both network administrators and attackers, depending on their objectives.
Usage:
- For Network Administrators:
- Conducting network inventory.
- Managing service upgrade schedules.
- Monitoring hosts and service uptime.
- For Attackers:
- Identifying live hosts on the network.
- Discovering open services.
- Gathering information on packet filters and firewalls.
- Extracting MAC details and OS information, including their versions.
Key Features of Nmap:
- Capability to scan vast networks efficiently.
- Pre-installed in Kali Linux.
- Includes a GUI version called Zenmap for ease of use.
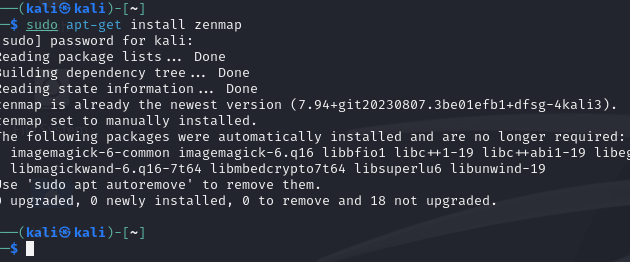
Installation:
To install Zenmap on Linux, use the following command:
for windows visit the official website https://nmap.org/download.html
TUTORIAL ON HOW TO USE NMAP
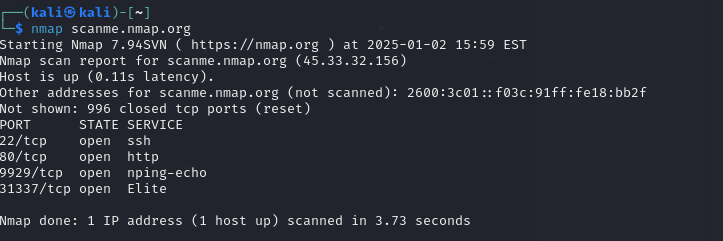
We will be using the official Nmap scanning site, scanme.nmap.org, to learn how to use Nmap. Let’s start with the CLI commands.1. Scan a Single Target
To scan a single target, use the following command
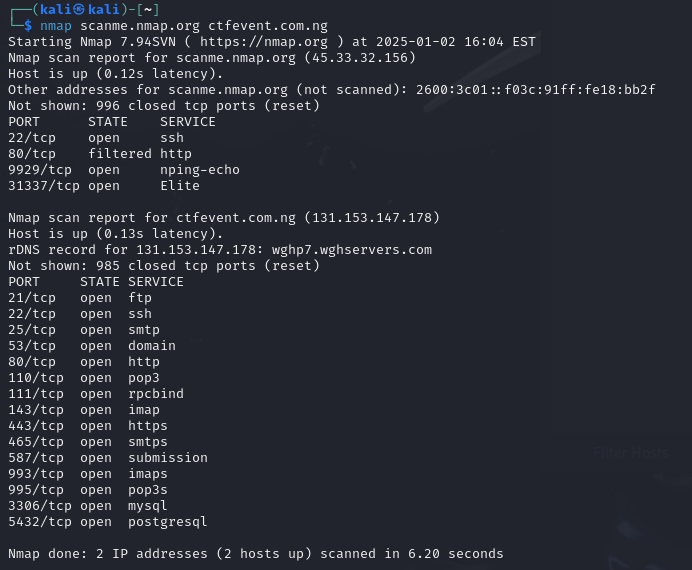
2. Scan Multiple Targets
To scan multiple targets, use the following command:
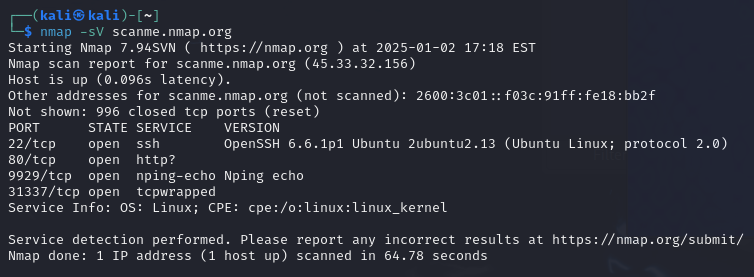
3. Detect Service Version
To detect the versions of services running on open ports, use the following command:
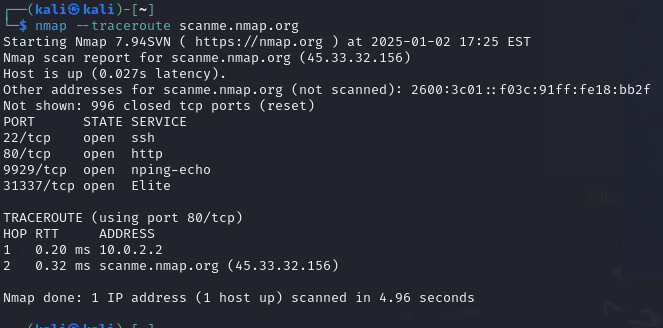
4. Perform a Traceroute
To perform a traceroute and map the path packets take to the target use the following command :
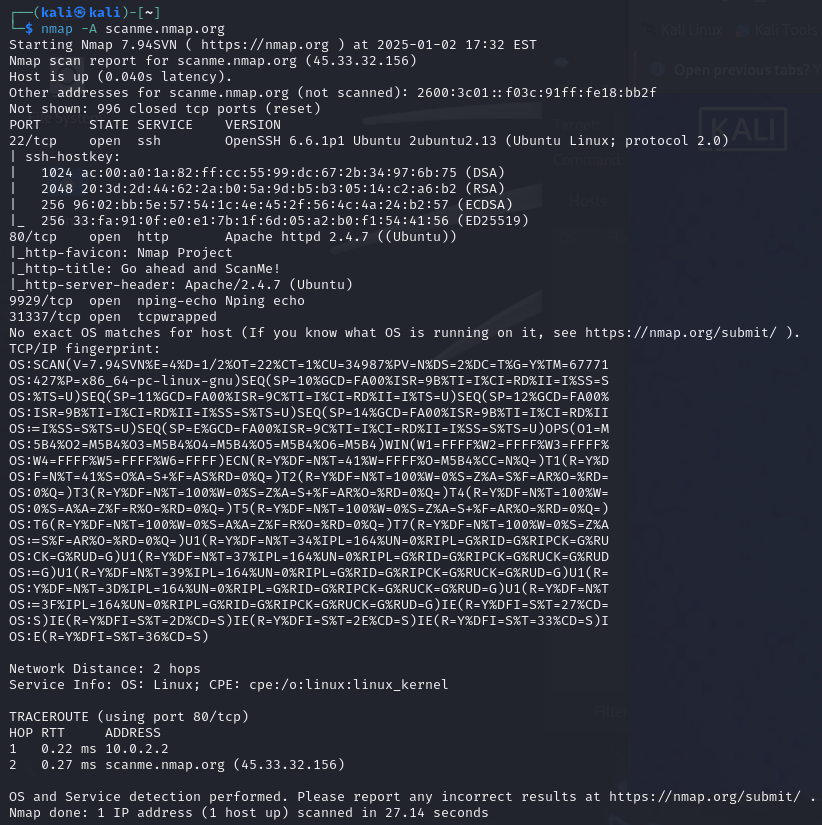
5. Perform an Aggressive Scan
To perform an aggressive scan that combines multiple options like OS detection, service version detection, and traceroute, use the following command:
The commands above are just a few examples.
For a comprehensive list, you can download it using and also you can visit the offical nmap website to learn more this link. Additionally, you can visit the official Nmap website to learn more
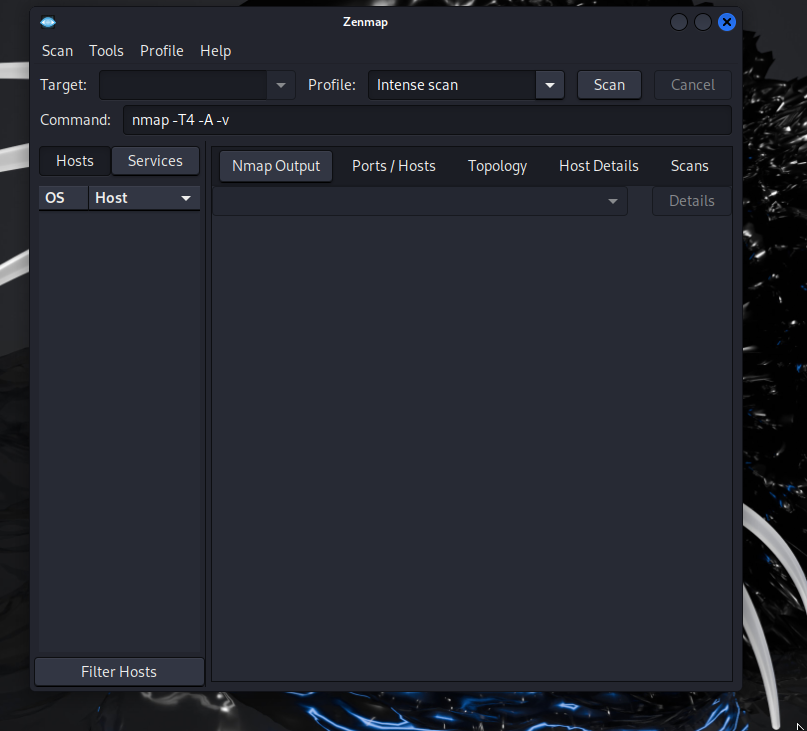
TUTORIAL ON HOW TO USE ZENMAP
well zenmap is a gui an is easy to there are options of scan and also we can also edit the command to for our desiered scan also options
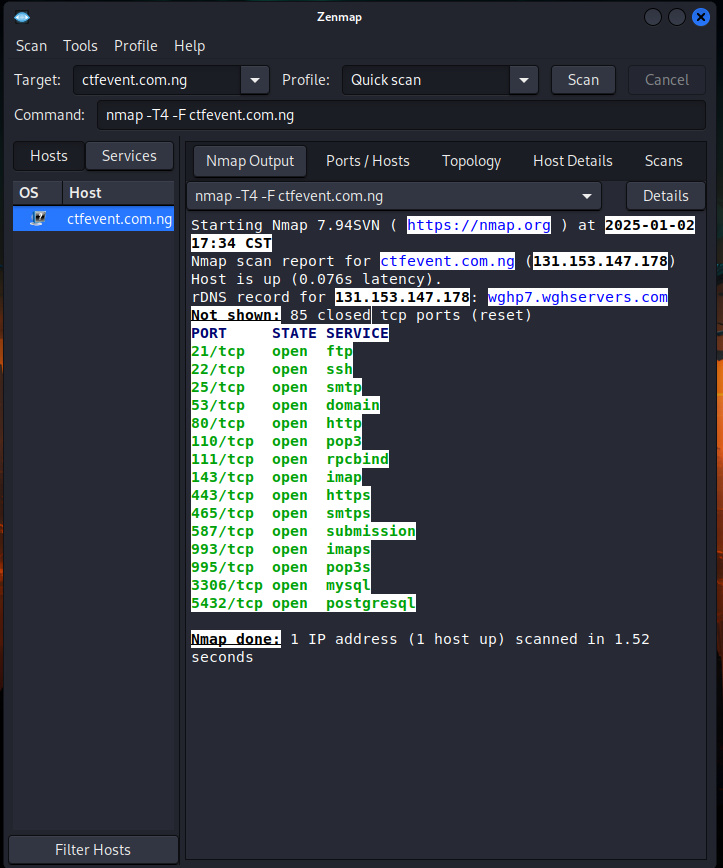
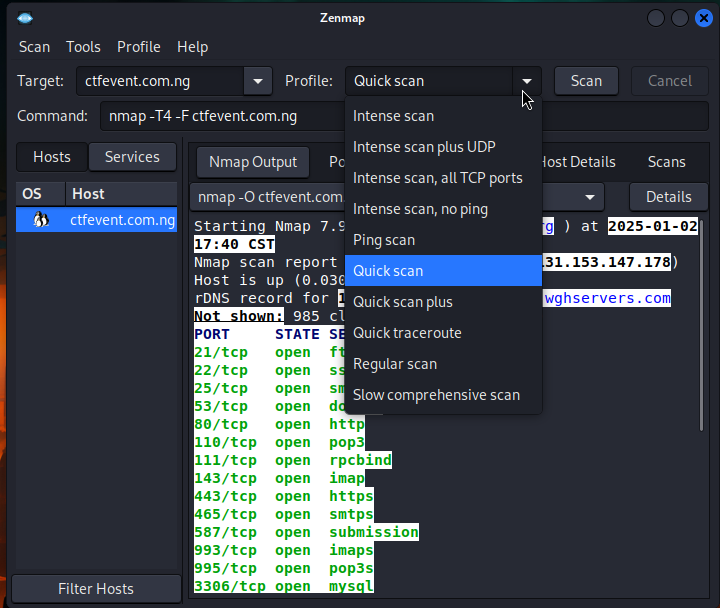
The profile Option is where to specify type of scan
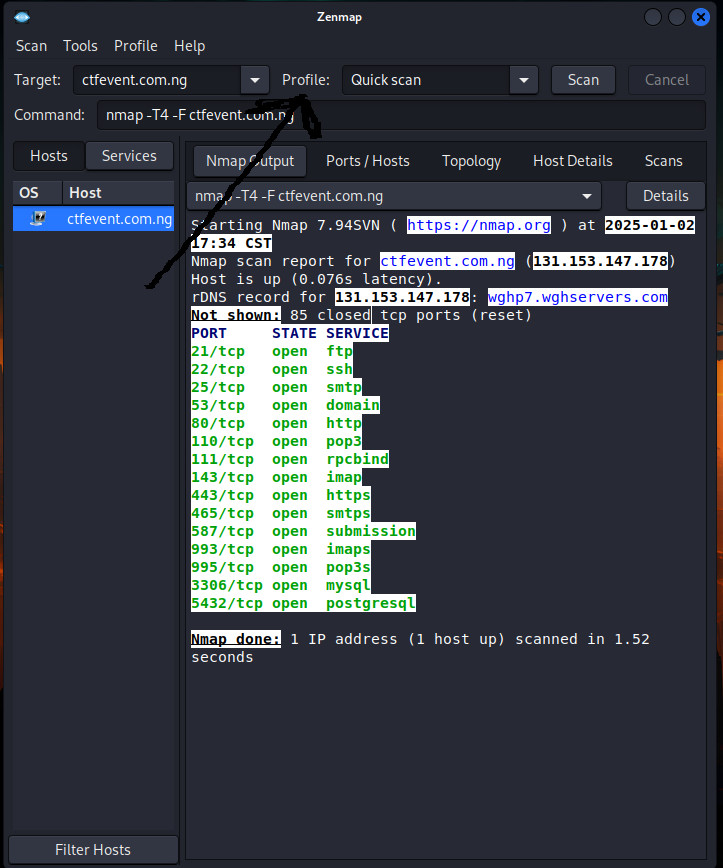
These are options avaiavble
With Zenmap, you can edit commands to suit your needs. For example I am editing the command to an operating system scanning.
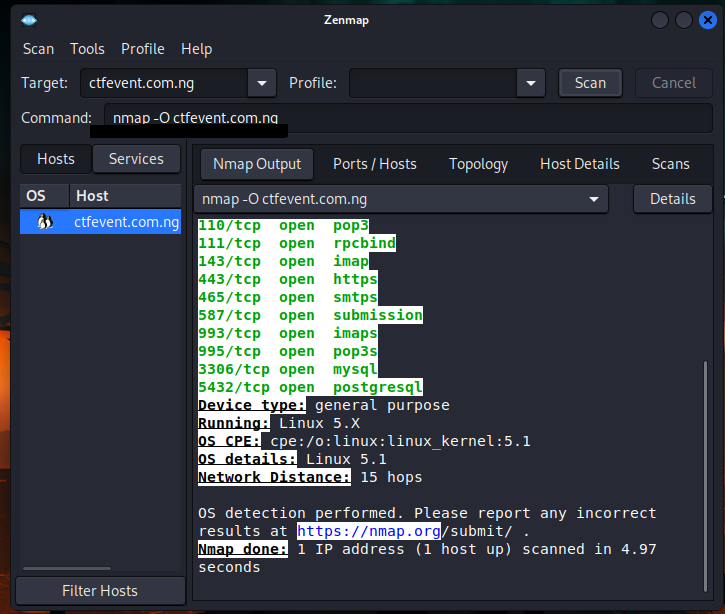
From the above example, you can see how I used the -s command in the command option to enable operating system scanning. Similarly, you can always update and customize it to include any command you desire, depending on the specific scan you want to perform.
